Simulating Iranian APT Attacks Against Middle East Governments
Minute Read

TL;DR
An Iranian nation-state actor compromised Middle East government infrastructure and operated undetected for nearly two years. The attackers deployed web shells on Exchange servers, established over 15 scheduled tasks for persistence, harvested credentials via password filter DLLs and LSASS dumping, moved laterally using built-in admin tools, and exfiltrated executive mailboxes over encrypted HTTPS channels. This article breaks down each phase of the attack, maps it to the MITRE ATT&CK framework, and shows how continuous breach and attack simulation with Thawd's Simlight platform can detect these TTPs before real adversaries exploit them.
Introduction
Do you know what modern cyber-attacks against government institutions actually look like? Recently, Fortinet released a comprehensive threat intelligence report detailing a long-running nation-state intrusion attributed to an Iranian threat actor targeting critical infrastructure in the Middle East. This article explores the technical progression of that attack and how the attackers operated for almost two years without detection.
Today’s advanced threats rarely rely on loud or immediately disruptive techniques. Instead, sophisticated adversaries operate quietly in the background: harvesting credentials, deploying backdoors, escalating privileges, and positioning themselves for future operations while remaining largely invisible. For this reason, one of the most effective ways to defend against modern adversaries is to simulate their techniques and continuously stress-test security controls before real attackers do.
This article summarizes the TTPs leveraged by the APT and demonstrates how effective simulation ensures that such TTPs are prevented and detected as early as possible in the attack chain.
Leveraging IIS & Exchange for External Access
The attackers relied heavily on ASPX web shells deployed on Exchange and IIS servers, turning public-facing infrastructure into their long-term command-and-control layer. Within one day of intrusion, they installed an advanced obfuscated web shell that enabled file browsing, command execution, file upload/exfiltration, timestamp manipulation, and system profiling.
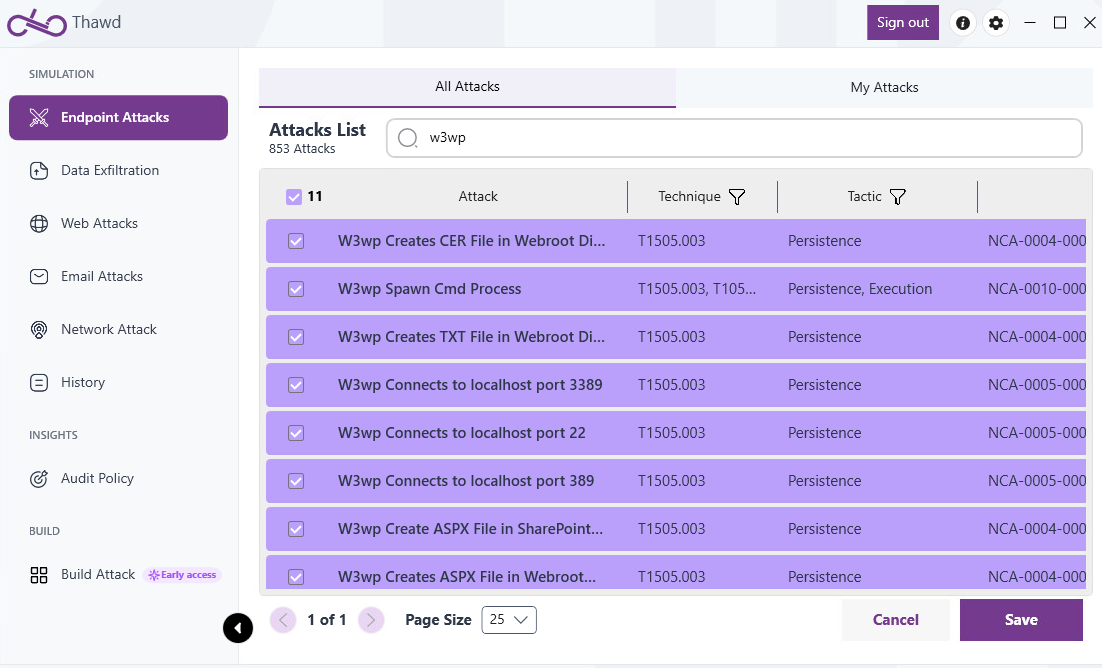
Because the web shells operated over normal HTTP traffic, activity blended with legitimate Exchange traffic, making detection difficult. The IIS worker process (w3wp.exe) became the main execution point for early attacker activity. Continuous validation of web shell detection capabilities could have identified this intrusion much earlier.
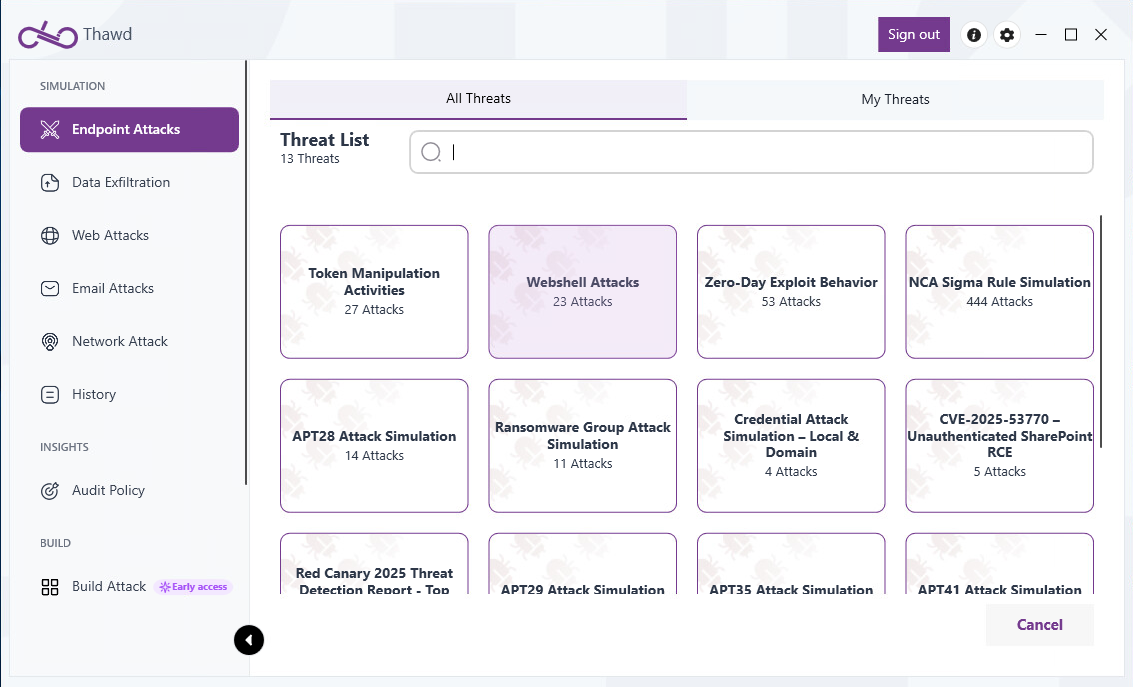
Thawd Insight: This multi-year intrusion could have been detected much earlier if defenders had continuously validated their ability to prevent and detect web shell behaviors. Security teams can expose control gaps before attackers do by simulating real-world web shell techniques like file system manipulation, command execution from IIS processes, and tunneling attacks. For this reason, we have added more than 30 behavioral web shell simulations to our breach and attack simulation platform to reflect the exact techniques observed in campaigns like this one.
Resilient Persistence Methods
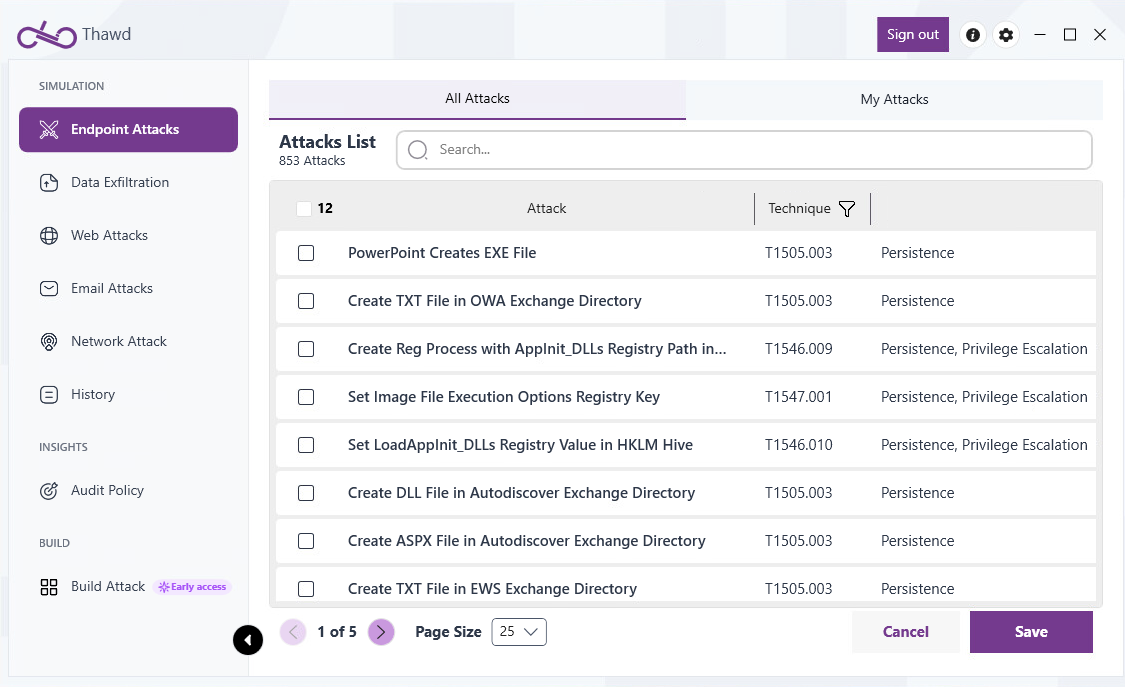
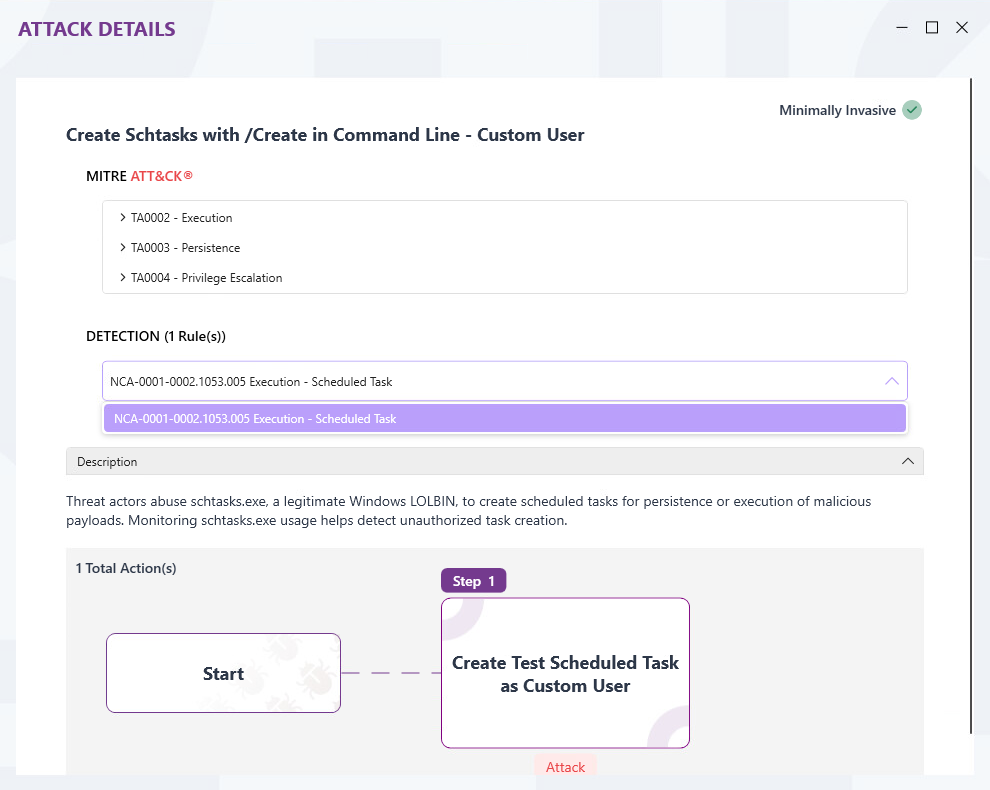
The attackers built redundant persistence to survive remediation. They deployed eight web shells and over fifteen scheduled tasks disguised as legitimate Windows components. These tasks launched both open-source frameworks and custom backdoors, ensuring execution after reboots or credential resets.
At least five distinct backdoor families were identified. Effective detection requires behavioral monitoring of scheduled task creation and abnormal execution patterns rather than relying on static indicators.
Thawd Insight: Effective detection of persistence mechanisms such as scheduled tasks must focus on behavioral patterns rather than static indicators like task names or file paths, which attackers can easily modify. Our breach and attack simulation platform exercises multiple scheduled task creation and execution techniques — including those observed in this campaign — allowing defenders to continuously validate their ability to detect stealthy persistence in real-world conditions.
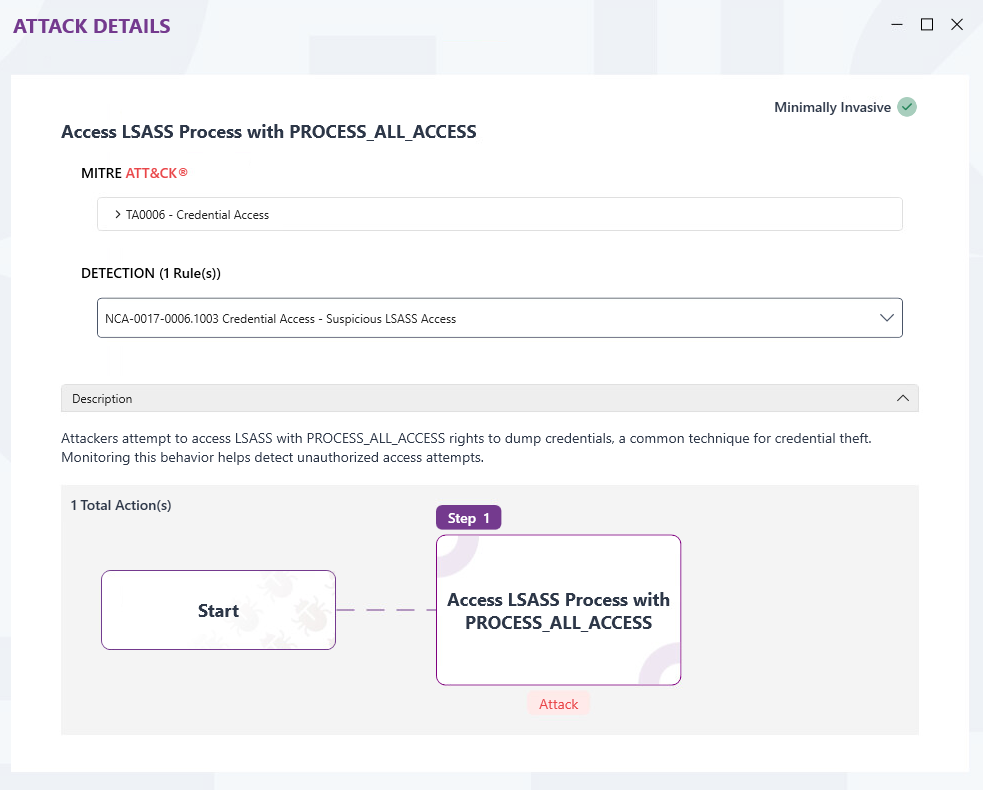
Multiple Credential Access Methods
The adversary continuously harvested credentials to maintain flexibility. They installed malicious password filter DLLs on domain controllers to intercept user logins, capturing credentials for over a year.
They also dumped LSASS memory using tools like Mimikatz and NanoDump to obtain plaintext credentials, hashes, and Kerberos tickets. Detection should focus on behavioral indicators such as abnormal LSASS access, unauthorized DLL registration, and credentials written to unusual locations.
Thawd Insight: Detecting credential abuse of this nature requires focusing on behavioral signals rather than specific tooling. Unauthorized access to LSASS memory, abnormal DLL registration within authentication providers, and credential material being written to non-standard locations all represent high-fidelity indicators of compromise. Our breach and attack simulation platform exercises both memory access abuse and authentication pipeline tampering, allowing organizations to continuously validate their ability to detect credential theft techniques before attackers leverage them in real campaigns.
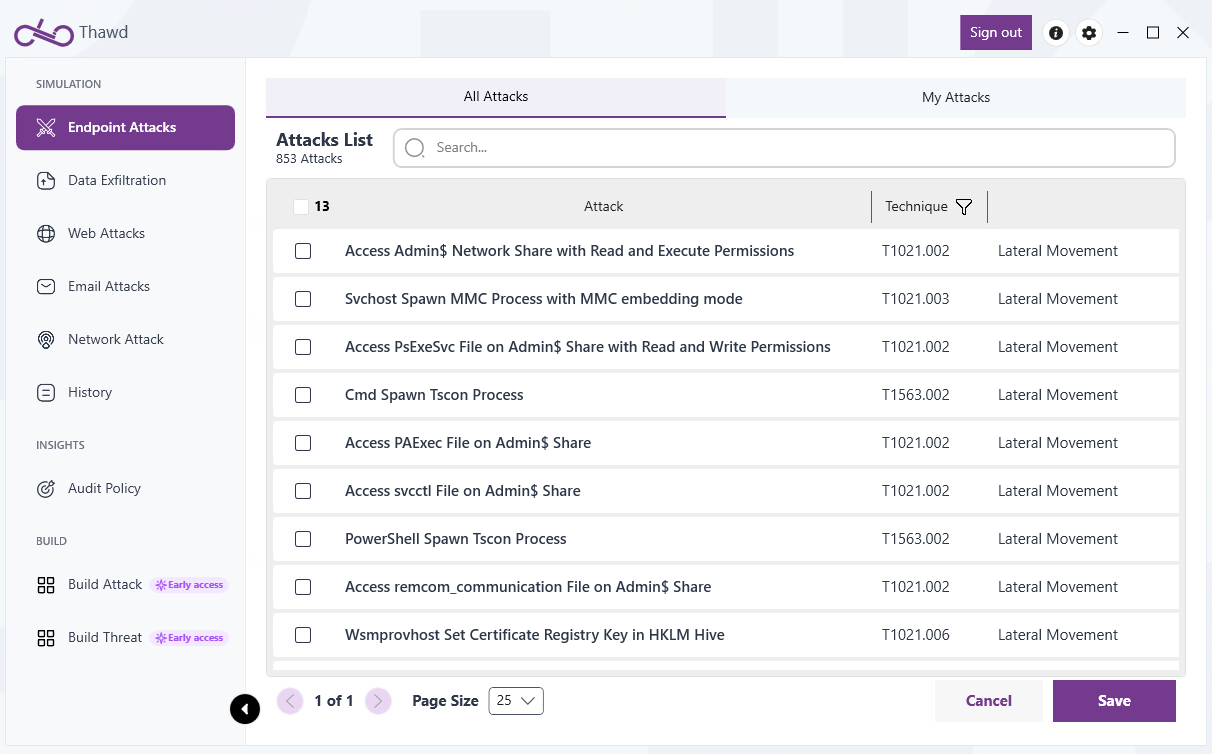
Lateral Movement Methods
To expand access, the attackers used legitimate tools including RDP, PsExec, and PowerShell Remoting. These techniques allowed interactive control, rapid command execution, and remote access without dropping additional malware.
Since these are standard administrative tools, detection must focus on abnormal authentication paths, unusual remote execution patterns, and movement from systems not typically used for administration.
Thawd Insight: At Thawd, we focus on simulating attacker-style lateral movement to determine whether internal controls can detect unauthorized movement across the network. This allows organizations to identify blind spots in internal access monitoring before those gaps are exploited in a real intrusion.
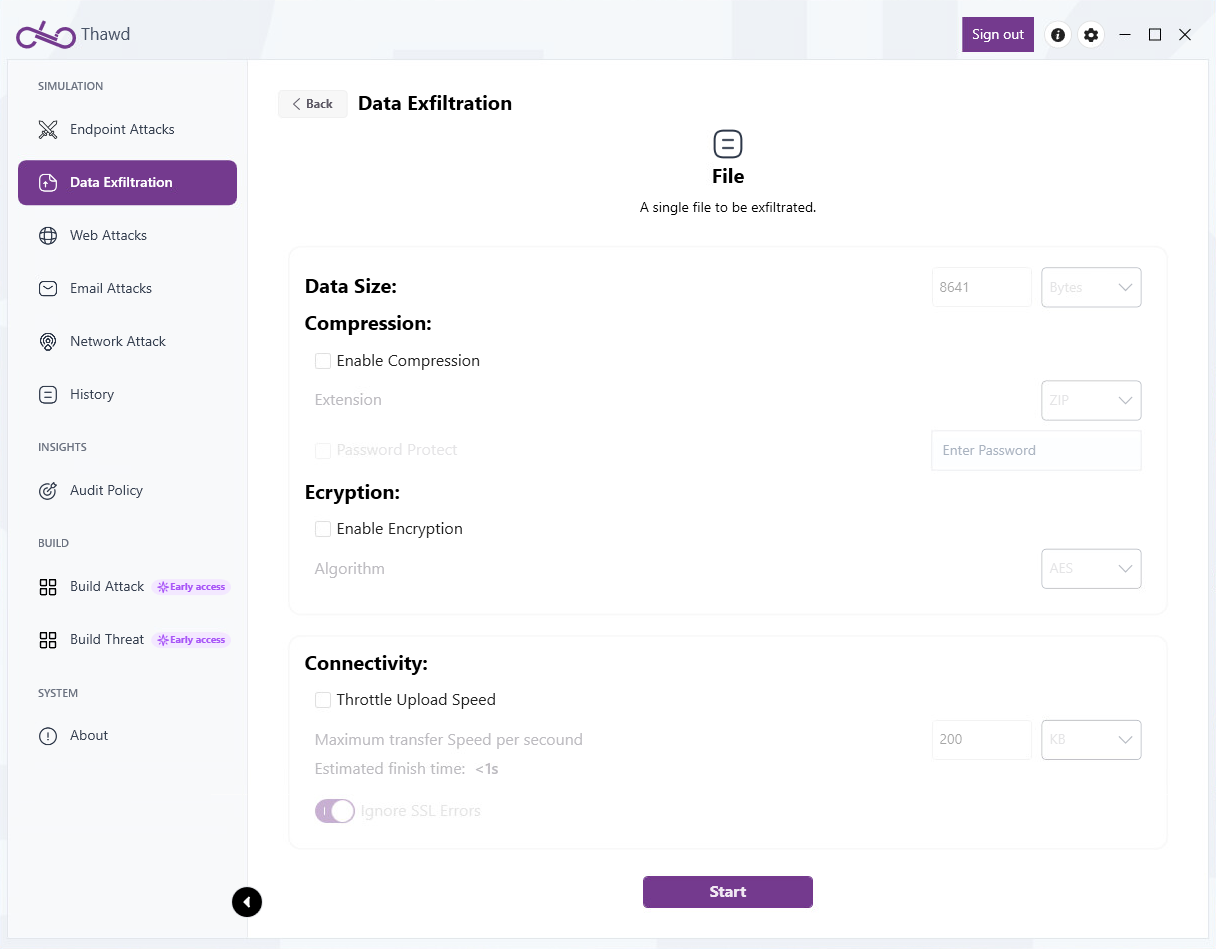
Exfiltration Methods
Sensitive data, including executive mailboxes, was staged and exfiltrated over HTTPS to blend with normal outbound traffic. Attackers leveraged native Exchange PowerShell modules to export mailboxes, then used base64 encoding, encryption, and chunked transfers to reduce the likelihood of detection.
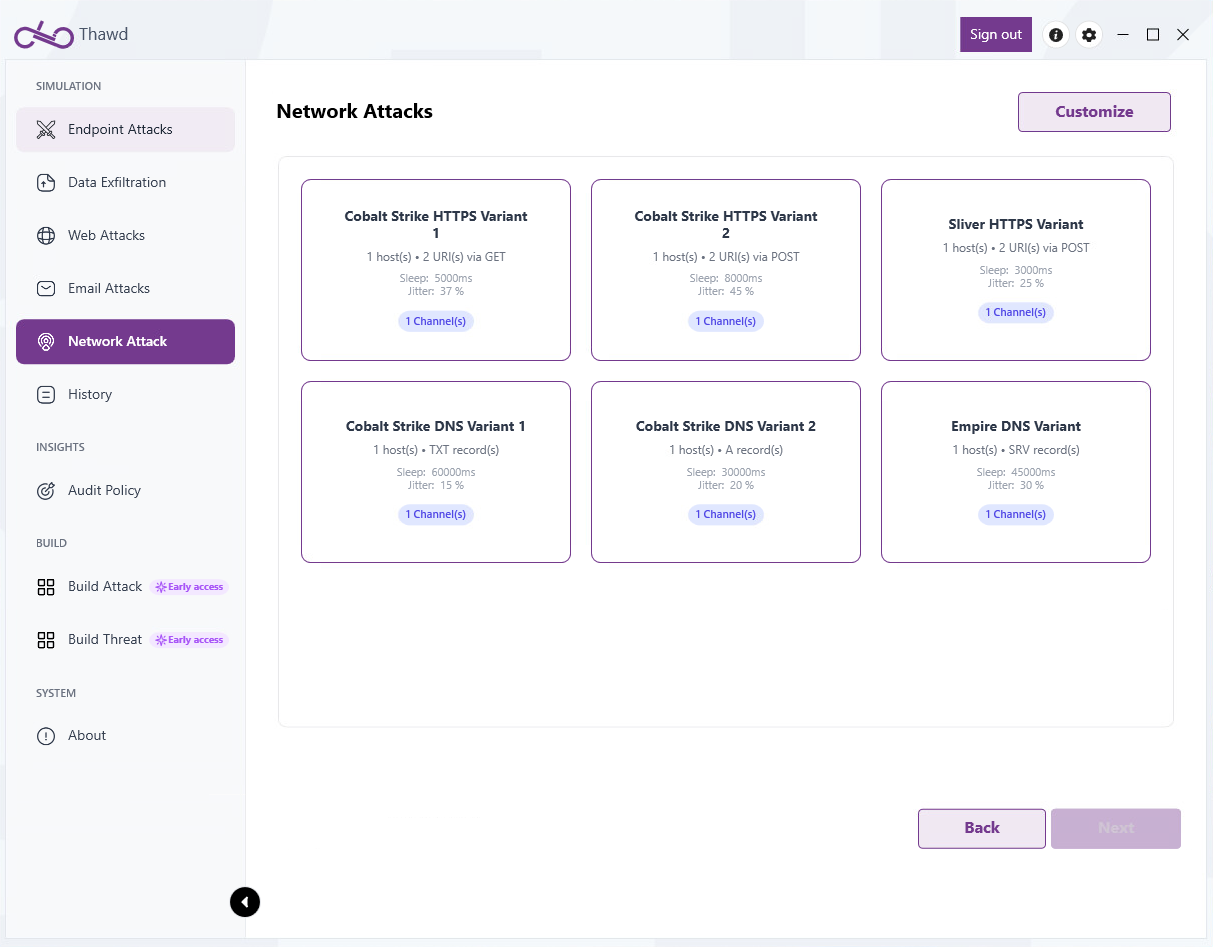
In parallel, multiple backdoors maintained periodic HTTP/HTTPS C2 beaconing to receive tasking and transmit collected data. By operating through legitimate protocols and trusted system processes, the adversary sustained remote control and exfiltrated information while generating minimal security alerts.
Thawd Insight: To validate defenses against covert data theft, our breach and attack simulation platform emulates data staging and exfiltration across multiple channels (e.g., HTTPS and SSH), chunked file transfers, and abnormal outbound traffic from infrastructure servers. In addition, the platform supports a wide range of staging techniques, including compression, encryption, and encoding.
Key Takeaways
1. Web shells remain one of the most dangerous persistence mechanisms. Operating over standard HTTP traffic, they blend seamlessly with legitimate web activity and can go undetected for months or years. Organizations must continuously validate that their security stack can detect web shell deployment and activity.
2. Redundant persistence is the norm for nation-state actors. With eight web shells and over fifteen scheduled tasks, this adversary ensured that no single remediation action could fully remove their access. Detection strategies must account for layered persistence across multiple vectors.
3. Credential theft is a long game. Password filter DLLs silently intercepted credentials for over a year. Combined with LSASS memory dumps, the attackers maintained a constantly refreshed pool of valid credentials. Behavioral detection of abnormal authentication patterns is essential.
4. Living-off-the-land makes lateral movement nearly invisible. By using RDP, PsExec, and PowerShell Remoting tools already present in any Windows environment the attackers avoided deploying detectable malware for lateral movement. Defenders need to baseline normal admin behavior and alert on deviations.
5. Continuous simulation is the best defense. Static, point-in-time assessments cannot keep pace with adversaries who evolve their tradecraft. Regularly simulating the full attack chain from initial access through exfiltration is the most effective way to identify and close detection gaps before they are exploited.
Book a Demo and See the Difference
Two years. That’s how long this adversary operated undetected inside critical government infrastructure harvesting credentials, exfiltrating executive communications, and expanding their foothold across the network.
The question isn’t if your organization will be targeted. It’s whether your defenses will catch it when it happens.
Thawd’s Simlight platform delivers continuous, real-world attack simulations designed by our engineers and threat researchers. Every technique covered in this article from web shell deployment to credential theft to covert exfiltration can be safely simulated against your production environment to reveal exactly where your defenses hold and where they break.
See how Simlight can help you find the gaps before adversaries do.
Related articles


What is SOC Readiness?

What is Adversary Emulation?

See Thawd In Action






